
Defend IT Assets and Classified Data
Certified for the defence sector
With a longstanding track record of delivering results in the Ministry of Defence supply chain, we’re your proven partner for Secure Destruction that meets the rigorous demands of the Defence sector.
By choosing Restore Technology, you choose a data destruction partner ready to operate securely, at scale, with complete confidence in confidentiality.

How do we carry out Secure Destruction of data?
We can work at your site in secure, self-contained vehicles, or off-site at one of our Government-approved facilities. Our team conducts a formal chain-of-custody transfer before reducing assets to the desired shred size, as small as 2mm.
All items are audited before destruction to ensure full compliance, and any shredded materials are securely transported for compliant recycling.

Our Certifications & Standards
- Certified by NPSA and NCSC CAS-S to the highest level.
- Cyber Essentials and Cyber Essentials Plus accredited.
- JOSCAR approved.
- Full Waste Management Permit.
- ISO9001 / ISO14001 / ISO45001 / ISO27001
Here’s what makes our services ideal for your defence sector operation:
Fully-compliant destruction
Our highly experienced, vetted team can deliver fully compliant destruction of any Electronic Storage Media (ESM) at all Government security classifications.

Government-approved facilities
We can deliver secure destruction of data either on-site at your premises, or off-site at one of our Government-approved facilities.

Nationwide capability
Benefit from our nationwide coverage, which includes access to the UK’s largest fleet of specialist and self-contained destruction vehicles.

Fully documented audit trails
Rest assured all bases are covered. Working with us, you’ll receive the paperwork you need throughout the process, including: CODD (Certificate of Onsite Data Destruction), HWCN (Hazardous Waste Consignment Note), a Serialised Audit, and a Certificate of Job Completion.

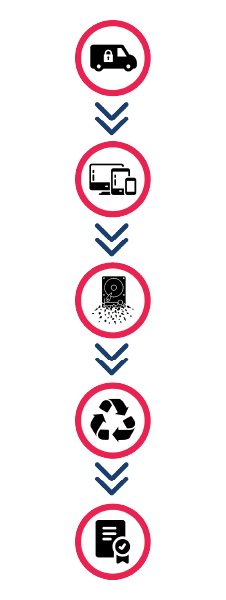
Our Secure Asset Destruction Process:
A vetted team is deployed to site in our secure, self-contained vehicles.
Upon arrival, a formal transfer of custody takes place as assets are collected from the client’s premises and prepared for processing.
Destruction activities commence immediately with our secure vehicles, ensuring assets never leave site intact.
All items are audited prior to destruction and verified post to ensure destruction is in line with agreed requirements and compliance.
Shredded materials are transferred under control to our premises for compliant recycling.
What else can we do:
There’s more to Restore Technology than Secure Destruction. A lot more, in fact. Through our nationwide coverage and extensive capabilities, we can support you through the entire IT lifecycle – click a link below to learn more.
Our Services





