There’s no end to the deviousness of data thieves when it comes to their will to steal and damage business reputations, and access cards and badges are among their prime data-bearing targets. Time to batten down on your security measures.

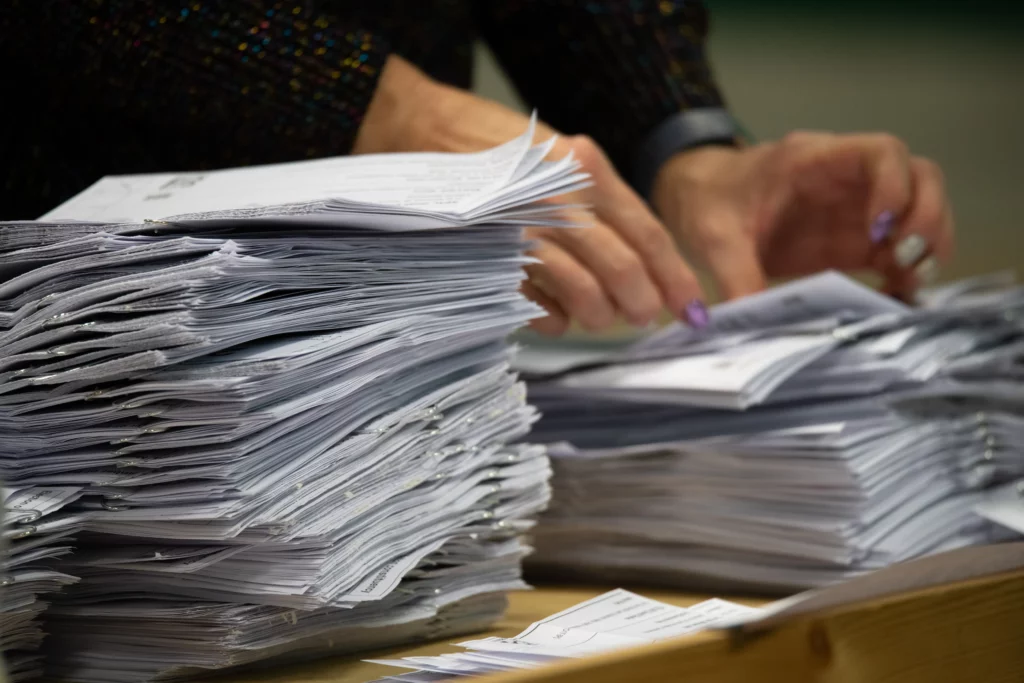
Many of us are now in lockstep with data protection legislation when it comes to the secure destruction of obsolete paper and digital information and even other company assets such as old uniforms, counterfeit and prototype products. All items that may reveal information that’s confidential to your colleagues, customers and business secrets, in fact.
But how much do you recognise the threat posed by physical access items, such as ID badges, cards and digital keys? According to the Mayweather Group*, up to 10% of malicious data breaches are caused by compromises to physical access defence lines, and around 60% of companies have reported this type of breach in the past five years. That’s a high failure rate for what is frequently the first wall in a business’ security set-up.
Facts about physical security breaches
With off-the-shelf kit, a data thief can scan and produce a clone of an RFID (Radio Frequency Identification Card) or NFC (Near Field Communication) card without even needing to take the original card. Once the info from the chip embedded in the card is copied, the perpetrator enjoys the same access as an authorised employee. The more sophisticated the access item, the more the layers contained within it can pose a problem. For example, with a stolen card, hackers can follow you through secured access doors (called ‘tailgating’) and gain entry to locations such as server rooms or into office spaces where they can install malware and steal hardware. Through cloning or theft, these data robbers can use individuals’ personal information – even just a name and job title will do – to infiltrate your company hierarchy and launch phishing scams or falsify identities.
Our servicesWhat methods of protection are there?
Employee education about the risks
Systems and processes for reducing those data protection risks
Strict visitor policies
Anti-tailgating entry points
Encrypted RFID/NFC cards
Tracking and monitoring access use
Managing access technologies for obsolescence.

You can take all these measures, but there should, in truth, be one further point.
Ensuring secure disposal and destruction of redundant access items.
In our opinion, you can have all the company policies and fully educated, compliant employees possible, and yet a poorly executed disposal method for old or no-longer-needed access items could expose your organisation to bad actors just the same.
The Restore Datashred solution
At Datashred, ‘security’ is our middle name, and our solution is simple: don’t let access item disposal become your weakest link.
Use our professional secure collection and shredding services to ensure your business’ confidentiality and reputation throughout your systems and processes.
Our range of adaptable shredding and disposal services for businesses is built on meeting the standards laid down by legislation such as the UK GDPR and Data Protection Act 2018, as well as sector-specific regulations from the FCA and NHS Information Governance standards, and the Freedom of Information Act 2000. In addition, our ISO 27001 and ISO 14001 accreditations, among others, ensure every item we destroy is done so securely and ethically.
In short, you can trust us to meet, and exceed, the security and environmental requirements of any sector. Here’s how.
At Restore Datashred, we provide:
On-site and off-site shredding
Which we design around you and your security needs.

Secure on-site storage
Featuring collection bins ranging from under-desk Shred Boxes and lockable cabinets to secured wheelie bins and, if necessary, fortress level containers. All designed to be part of your business’ data protection set-up, keeping old, no-longer-needed cards, badges, and so on, safe until collected by one of our team.

Trained security operatives
Professionals working to BS5878 standard to ensure the safety and privacy of your data from your place to our shredding blades.

State-of-the-art shredding
Whether in one of our high-speed mobile shredding trucks or at one of our modern high-security facilities, our machines reduce your access assets to 2mm shreds in seconds.

Complete audit trail
Which includes e-audited, barcoded shredding bins and sacks, GPS-tracked vehicles and a certificate of destruction to close the loop and provide peace of mind after each transaction.

Monitored destruction centres
With passworded entry protocols and 24/7 CCTV.

Don’t let what is supposed to be a security check item become a hazard to your data protection and integrity.
Give one of our Customer Service Hub team a call directly on 0330 029 7538 or contact them through the online customer form and find out how to seal your organisation’s protective ringfence with the missing piece of the security jigsaw: secure shredding and responsible disposal of your obsolete access items.
Get in touch Customer Login
Customer Login